Solana memecoin launchpad BONK.fun suffered a security breach after attackers hijacked a team account and used that access to compromise the platform’s domain. According to statements from the team and operator SolportTom, the attackers planted a crypto drainer on the BONK.fun website, creating a dangerous situation for users who visited the site after the breach.
The incident quickly drew attention across the Solana and broader crypto communities. The breach also highlighted a familiar problem in digital asset markets. Even when protocols and trading systems improve, attackers still target the user-facing layers that people trust every day.
What Happened?
BONK.fun and Tom both warned users not to interact with the domain once the team discovered the compromise. BONK.fun wrote, “A malicious actor has compromised the BONKfun domain. Do not interact with the website until we have secured everything.”
Tom issued a more detailed warning, saying hackers had “hijacked a team account, forcing a drainer on the DOMAIN.”
That description points to a frontend compromise rather than a breakdown in the underlying token infrastructure. Attackers appear to have gained control over an account connected to the platform’s domain operations, then used that access to serve malicious prompts through the official website. In practical terms, users who trusted the legitimate domain could have encountered a fake message that asked them to sign a terms of service prompt. That signature reportedly triggered the drainer.
Visitors who attempted to access the site later encountered browser security warnings that flagged the page as malicious and unsafe.
Who Was Affected?
Tom said the breach did not affect every BONK.fun user, clarifying that only users who signed the fake terms of service message on the compromised BONK.fun domain after the incident suffered losses.
Several users on X also claimed that they lost funds after interacting with the compromised website. One user wrote, "my account with 100k in it is gone. will it show up later?"
Data shared by blockchain analytics platform Bubblemaps suggested the impact remained relatively small, linking 13 wallet addresses to the attacker, estimating that about 35 users had been exploited with roughly $23,000 drained in total.
Bubblemaps noted that the figures rely on public onchain data and user reports. Some individuals claimed losses of more than $100,000, but the researchers said they could not find onchain evidence to confirm those larger claims.
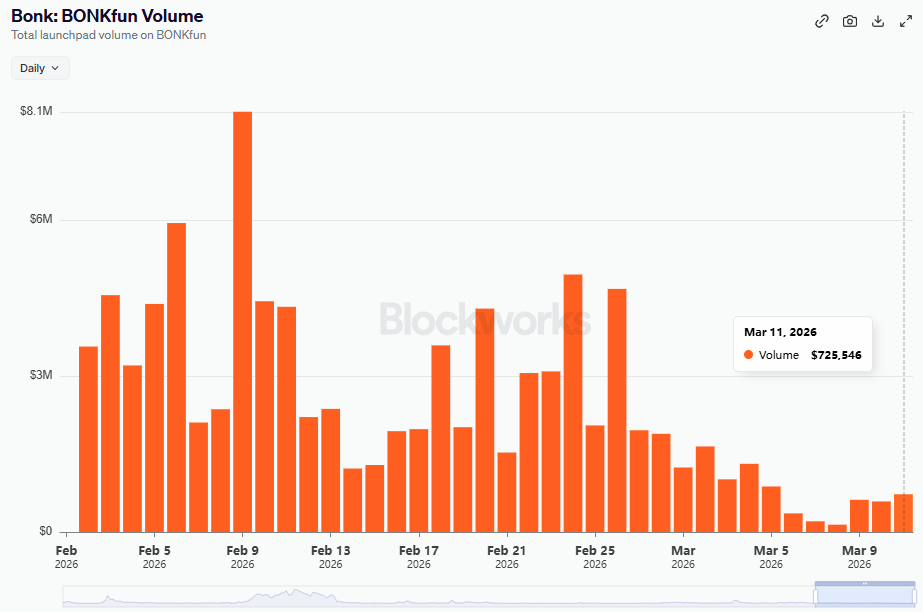
At the same time, available activity data suggests that the overall scale of the incident may have remained limited. BONK.fun’s share of launchpad activity had already been relatively small in the days leading up to the breach. Dune data shows that the platform launched 314 tokens in the last seven days, with only one token graduating during that period.
Over the previous three days, the platform launched 165 tokens and recorded zero graduates. Trading volume also remained modest and had been trending downward in the days leading up to the incident., with Blockworks data showing BONK.fun generating about $725,546 in volume on March 11, the day the incident occurred.
Community Reaction
At the same time, the incident triggered frustration and skepticism from parts of the community. Some users questioned how attackers gained access to the domain in the first place.
Others criticized the platform’s operational security and argued that the event damaged BONK.fun’s credibility.
These reactions reflected a broader pattern in crypto, where users expect platforms to protect not only smart contracts and treasury assets, but also domains, team accounts, and every part of the interface that touches end users.
“Crypto’s Newest Vulnerability Is Authorization”
The BONK.fun breach fits into a wider pattern of crypto attacks that rely on deception, malicious signatures, and trust abuse rather than code exploits alone. Attackers increasingly target wallets through phishing pages, impersonation tactics, fake approval prompts, and compromised websites. In cases like this one, the attacker only needs to convince a user to approve the wrong action.
That approach has become more important across the industry. A Nominis report on recent attacks have described an environment where phishing, malicious signatures, social engineering, and privileged access abuse often cause more financial damage than traditional smart contract flaws. In January 2026 alone, several major incidents showed how attackers increasingly target authorization and human behavior instead of relying only on technical exploits.
The broader trend suggests that operational security and user education now matter as much as smart contract audits in many situations.
Read More on SolanaFloor
Archer Exchange Launches CLOB Amidst Prop AMM Spoofing Concerns
Mastercard Rolls Out Global Crypto Partner Program With Solana, Paxos and Others
Inside Pump.fun's Ecosystem